In 2017, the National Cyber Security Centre (NCSC) published a detailed report examining the cyber crime business model – this report has been updated in 2023.
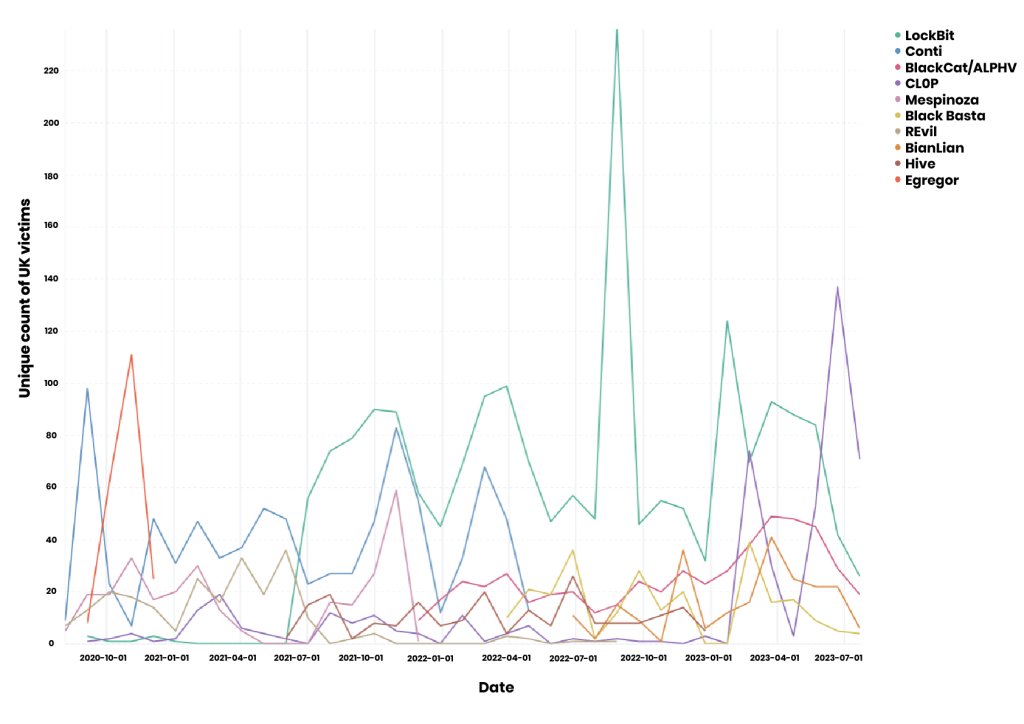
Since 2017, the growth in ransomware and extortion attacks has expanded dramatically, with cyber criminals adapting their business models to gain efficiencies and maximise profits.
The ransomware industry has evolved into a sophisticated supply chain that often defies western governments and leaves unprotected businesses on the back foot.
10 years after the first large-scale ransomware attack, nicknamed Cryptolocker, the industry has thrived on businesses’ weak online security.
This has enabled criminals to sell each other vulnerabilities or software weaknesses, create franchises with lower-skilled beginners and set up marketplaces to trade access to compromised businesses.
The assessment from the National Cyber Security Centre, which is part of GCHQ, and the National Crime Agency, comes as it has become increasingly clear that prosecutors in Russia, Belarus and a handful of other countries that were part of the former Soviet Union have little inclination to crack down on this lucrative crime.
Ransomware operators have also been detected in south-east Asia, India and west Africa.
“Traditional criminal justice outcomes are hard to achieve against actors based in uncooperative jurisdictions,” James Babbage, a director of general threats at the NCA, said in the report.
Instead, the US, UK and other allies have had to rely on technical means to dismantle some of the most prolific criminals, including a recent operation to take down the Qakbot network, which infected millions of computers with its malware, and sanctions against the creators of another one called Trickbot.
“This year we enforced two comprehensive sanction packages against more than a dozen Russian-speaking cyber criminals who targeted institutions across the world, including the NHS during the height of the pandemic,” notes The Rt Hon Tom Tugendhat, Minister of State (Minister for Security).
“The National Crime Agency worked alongside the FBI and German law enforcement to shut down a ransomware service, known as HIVE, which over two years extorted more than $100 million in ransom payments.
And we worked with 17 countries to take the Genesis Market (a go-to service which sold the personal data of millions of people to fraudsters) offline.”
Businesses could have deflected the many threats by improving their “cyber hygiene”, the reports says.
Often companies fail to have multi-factor authentication, an easily implemented industry standard, while others have weak passwords or do not update all their network’s computers.
“Implementing such measures would interrupt the majority of ransomware attacks,” the report says.
In some cases, US authorities have been able to seize cryptocurrency wallets, where the criminals receive their payments in exchange for the password that will decrypt information on their victim’s computers.
In recent months, the hacker group CL0P has hit dozens of western companies that rely on MOVEit software from US-based Progress Software.
The software was designed to keep confidential data secure and was used by businesses and institutions such as the BBC, British Airways, Boots and several US state government driving licence databases.
Now, on its dark web site, CL0P openly negotiates with its victims and shames those who refuse to pay by posting hundreds of gigabytes of payroll information, industrial designs and internal emails and documents.
Most payments are made secretly and in cryptocurrency, which is almost impossible to trace.
Estimates vary but the industry has expanded into a multibillion-dollar business.
One gang, Conti, made more than $180 million in 2021, the UK government has estimated, a sum that included at least £10 million from UK businesses.
The May 2021 attack on the Colonial Pipeline in the US, which disrupted oil prices and lasted weeks, was the most public example of the impact of ransomware on a business, but dozens are attacked daily, nearly all based in the west.
Detection by authorities has improved but cyber crime perpetrators are still ahead of governments and businesses in efficiency and speed, Sophos found.
The latest figures indicated that criminals take less than a day to steal data while it takes authorities on average five days to detect their malign presence on a network, compared with eight in 2022.
 trending
trending










Comments